Meraki Site-to-site VPN makes it easy to connect remote networks and share network resources. In the event that VPN fails or network resources are inaccessible, there are several places to look in Dashboard to quickly resolve most problems. This article will overview common site-to-site VPN issues and recommended troubleshooting steps.
- Meraki Vpn Settings
- Remote Access Vpn Definition
- Meraki Vpn Setup
- Meraki Remote Access Vpn Download
- Setup Client Vpn Meraki
Troubleshooting
- Cisco Meraki uses the integrated Windows client for VPN connection (no Cisco client at this time). To be able to connect with simple AD user account credentials, along with a simple pre-shared key, the steps are very simple.
- The VPN connects from a Windows 10 device but I can't ping or access anything on the remote network (Win10 firewall is disabled and network is set to private, also using a different IP range to the remote VPN network). The Meraki guide say's if you don't have any VLAN's or firewall rules in place, the VPN client's should be able to access.
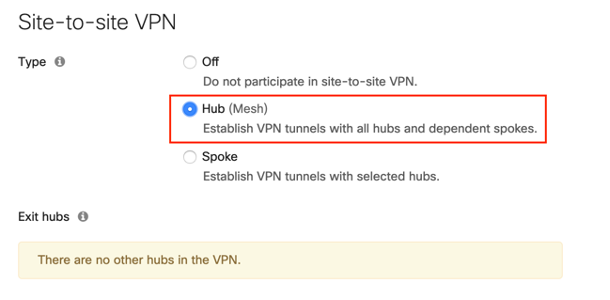
If there appears to be an issue with VPN, start by referencing the Security & SD-WAN > Monitor > VPN status page to check the health of the appliance's connection to the VPN registry and the other peers. If one specific tunnel is having issues, it may be helpful to check the status page for the networks of each peer in case one of them is offline or disconnected from the registry:
The following sections outline common issues with site-to-site VPN and recommended troubleshooting steps:
Can't ping or access network resources on the other network
When using Meraki hosted authentication, VPN account/user name setting on client devices (e.g., PC or Mac) is the user email address entered in the Dashboard. Open Start Menu Control Panel, click on Network and Internet, click on View network status and tasks.
If you are unable to connect to devices on the other network from your site:
- Are both devices online and connected to the registry?
- As outlined above, be sure to check the Security & SD-WAN > Monitor > VPN status page for each side's Dashboard network.
- Is the subnet you're trying to reach advertised over VPN?
- On the remote side's Dashboard network, navigate to Security & SD-WAN > Configure > Site-to-site VPN. Under Local networks, make sure the Use VPN toggle is set to Yes for the subnet you're trying to reach.You should also check these settings on your local site's Dashboard network to ensure that the subnet you're connecting from is also advertised.
- If using a full tunnel configuration, bear in mind that when specifying a prefix to be part of a VPN, everything covered by that prefix will be allowed in the VPN. Therefore, subnets that overlap will cause traffic in a more specific subnet to be sent through the VPN, even if it is not configured to be included in the VPN. For example, if 10.0.0.0/16 is configured to be included in the VPN but 10.0.1.0/24 is not, traffic sourced from 10.0.1.50 will still be sent over the VPN.
- Are any firewalls blocking this traffic on the network?
- In addition to any non-Meraki firewalls on the network that may be blocking this traffic (including firewalls that may be enabled on the device you're trying to access), check the Security & SD-WAN > Configure > Site-to-site VPN > Organization-wide settings section to see if there are any Site-to-site outbound firewall rules.
- Are there any problems reaching out to non-VPN peers?
- Try sending pings or traceroutes to public IPs (such as 8.8.8.8) or access public websites to see if the problem isn't strictly related to VPN.
- Try pinging the public IP of the other MX from your local network. If this fails but general Internet connectivity appears to be fine, there is likely an upstream ISP routing issue that is preventing the two sites from communicating directly even though they both have Internet access and are connected to the VPN registry.
- Are there routes configured on both sides that point to the remote subnets?
- If the MX is not the only gateway in the network (e.g. the MX is connected to a layer 3 switch or router with its own directly connected networks), any devices that are not using the MX as their gateway will need their traffic routed to the MX in order to send traffic across the VPN. Make sure any other routing devices on the network have a route that allows them to access the remote VPN subnets via the MX's local IP address.
- For extensive details on deploying the MX as a VPN concentrator, please refer to our VPN Concentrator Deployment Guide.
- Are these devices on non-overlapping subnets?
- If the device on each end is on a subnet that overlaps with the other side, the MX will be unable to route traffic to the other side as it will believe the traffic is destined for the local network. It is recommended to have unique subnets with no overlap on each network connected to the VPN.
- If identical networks are required on each side of a tunnel, you may need to enable VPN Subnet Translation. Please note that this feature does not allow for partial overlap between subnets, and is not supported with non-Meraki VPN peers.
Meraki Vpn Settings

VPN status page reports an unfriendly NAT or disconnected from VPN Registry
If the Security & SD-WAN > Monitor > VPN status page for a given network reports either 'NAT type: Unfriendly' or 'VPN Registry: Disconnected', there is likely a device upstream of the MX for that site that is preventing AutoVPN from working correctly.
- NAT type: Unfriendly indicates that the upstream NAT won't allow the MX to use UDP hole punching to form the tunnel. It is recommended to set NAT traversal to Manual: Port forwarding to bypass this issue.
- VPN Registry: Disconnected indicates that the upstream device is not allowing the MX to communicate with the VPN registry. It is recommended to configure any upstream firewalls to allow the traffic listed in Dashboard under Help > Firewall info.
For more information on these two error messages and VPN registry troubleshooting in general, please reference our documentation regarding Troubleshooting VPN Registration for Meraki AutoVPN.
Problems with VPN between Meraki MX/Z-series and a non-Meraki peer
If you are having issues with a non-Meraki VPN connection and the above troubleshooting tips did not resolve the issue, please reference our documentation regarding Troubleshooting Non-Meraki Site-to-Site VPN Peers.
1. Open Start Menu -> Search “VPN” -> Click Change virtual private networks (VPN).
2. From the VPN settings page, click Add a VPNconnection.3
3. In the Add a VPN connection dialog:
- Set the VPN provider to Windows (built-in)
- Provide a Connection name for the VPN connection.
- Specify a public IP address (found in Dashboard, under Security appliance -> Monitor -> Appliance status -> Uplink) or hostname for the Server name or address.
- Select L2TP/IPsec with pre-shared key for the VPNtype.
- Provide a User name and Password (optional).
4. After the VPN connection has been created, click Change adapter options under Related settings.
Remote Access Vpn Definition
5. Right-click on the VPN Connection from the list of adapters and click Properties.
6. In the Security tab, select “Require encryption (disconnect if server declines)” under Data encryption.
Then, select Allow these protocols under Authentication. From the list of protocols, check “Unencrypted password (PAP) Cleanmem free download. “, and uncheck all other options.

Despite the name “Unencrypted PAP”, the client’s password is sent encrypted over an IPsec tunnel between the client device and the MX. The password is fully secure and never sent in clear text over either the WAN or LAN.
7. Click on “Advances settings“
In Advanced Properties dialog box, choose “Use preshared key for authentication” and enter the same key you used for the client VPN settings in the Dashboard. Note: if you are enabling client VPN for your employees, you will need to distribute this key.
8. Back at the Network Connections window, right-click on the VPN connection and click Connect / Disconnect.
9. Find your VPN profile and click Connect.
Meraki Vpn Setup
10. Enter your user name and password. Click OK.
Meraki Remote Access Vpn Download
Was this article helpful?
Setup Client Vpn Meraki
Related Articles
